Password Protection in Microsoft Word. How to Add or Remove Protection, Crack Word Files
The only sure-fire way to secure an MS Word document from unauthorized access is to set a “Password to Open”. Only that kind of password guarantees that your data are securely encrypted and cannot be accessed without the password (in fact, it’s only true for some versions of Word).
All other security methods used in Microsoft Word protect more from careless actions than from unauthorized access. Regardless of the version of Word such passwords are easy to find and/or remove.
In this article we’ll show you how to enable, remove and recover a “Password to Open” in a Word document.
Setting a “Password to Open” in Word
Once you’re finished with a document and ready to save it you either simply save a file or encrypt your data with a password. If you choose to secure your file you can use the following two methods.
Method 1
1. Click the “File” menu, select the Info tab, then select the Protect Document button. Click Encrypt with Password.
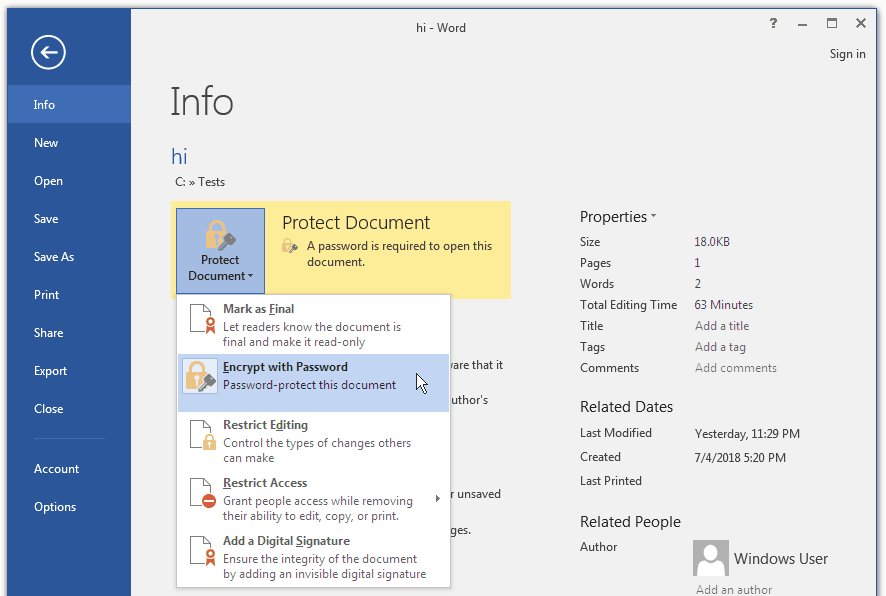
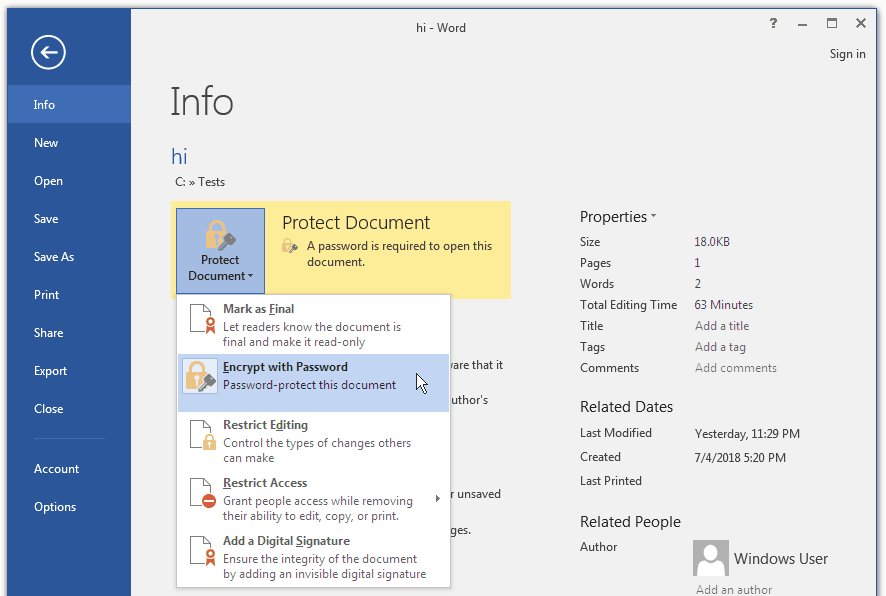
Fig. 1 : File encryption menu
2. In the popup box enter and confirm your password then click OK:
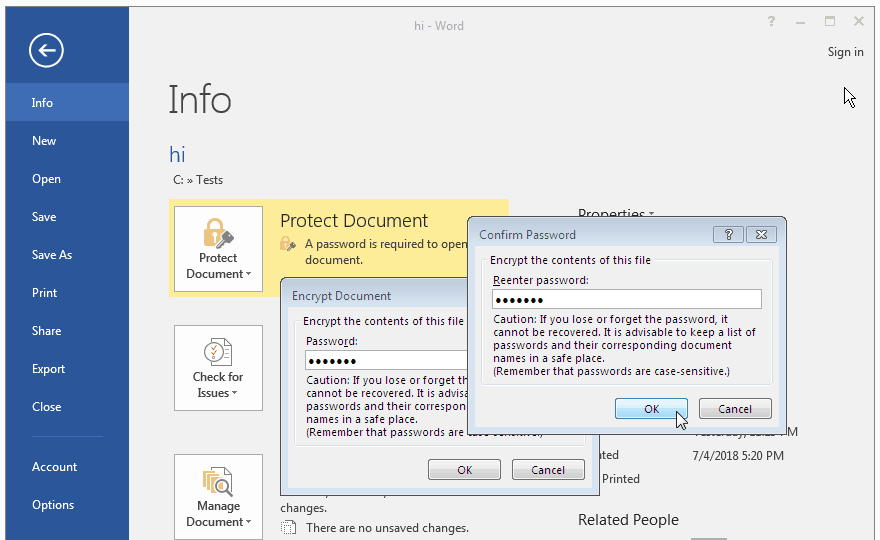
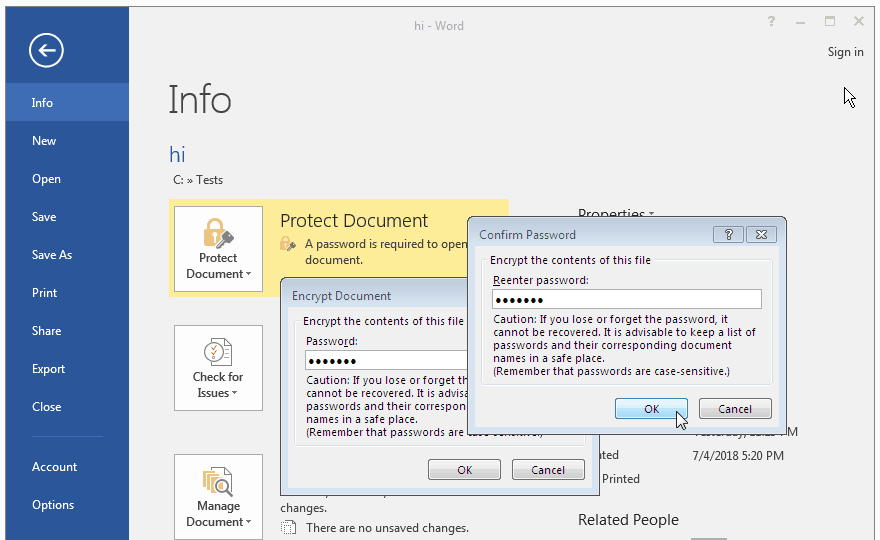
Fig. 2 : Popup box for entering password
Caution! If you lose or forget your password it may not be recovered (unless it’s a Word 97-2003 file).
3. Done! Your document is now protected, the data secured, you can save the file as usual. Each time you open the document, you will be prompted to enter your password to decrypt the data:
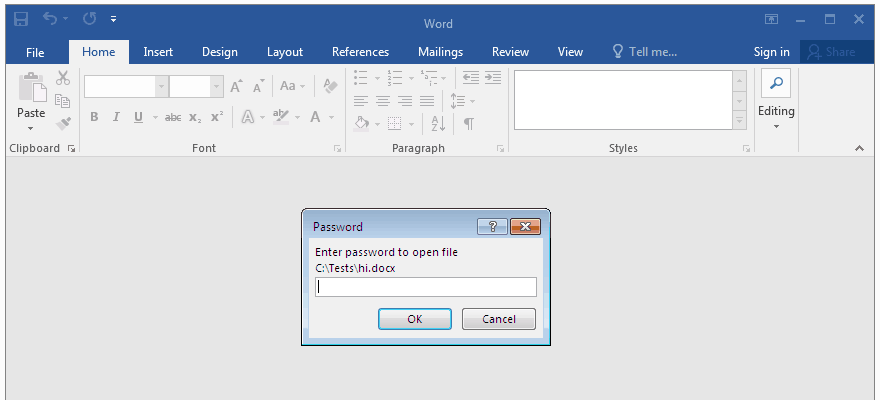
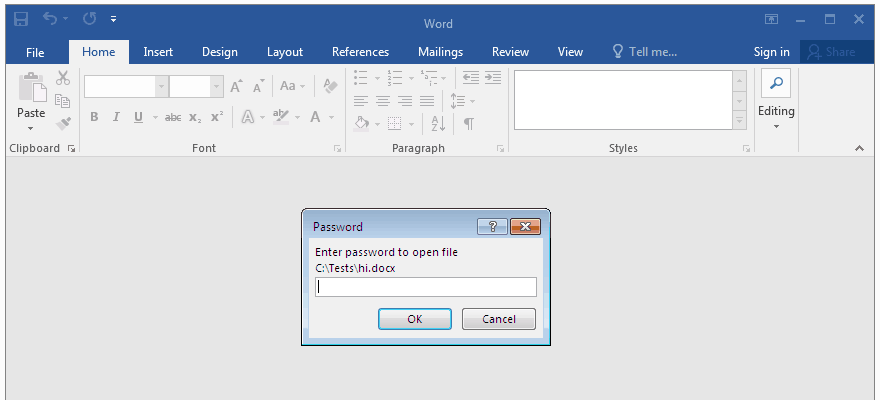
Fig. 3 : Opening a password protected file in Microsoft Word
Method 2
1. Go to Save As in the File menu and right there in the dialog box where you choose location and enter a new name for the file click Tools and choose General Options… in the drop-down list:
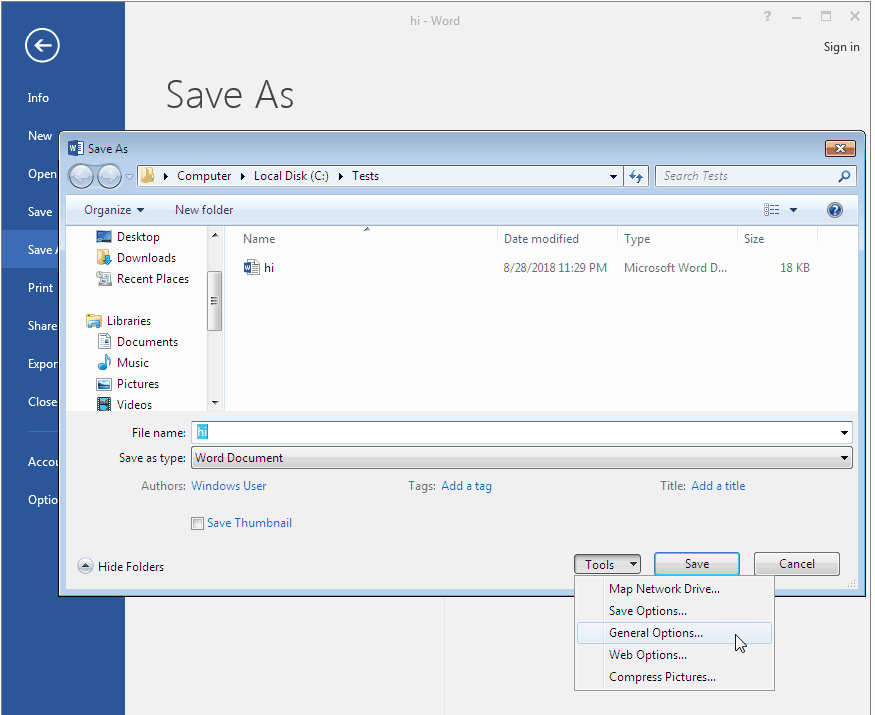
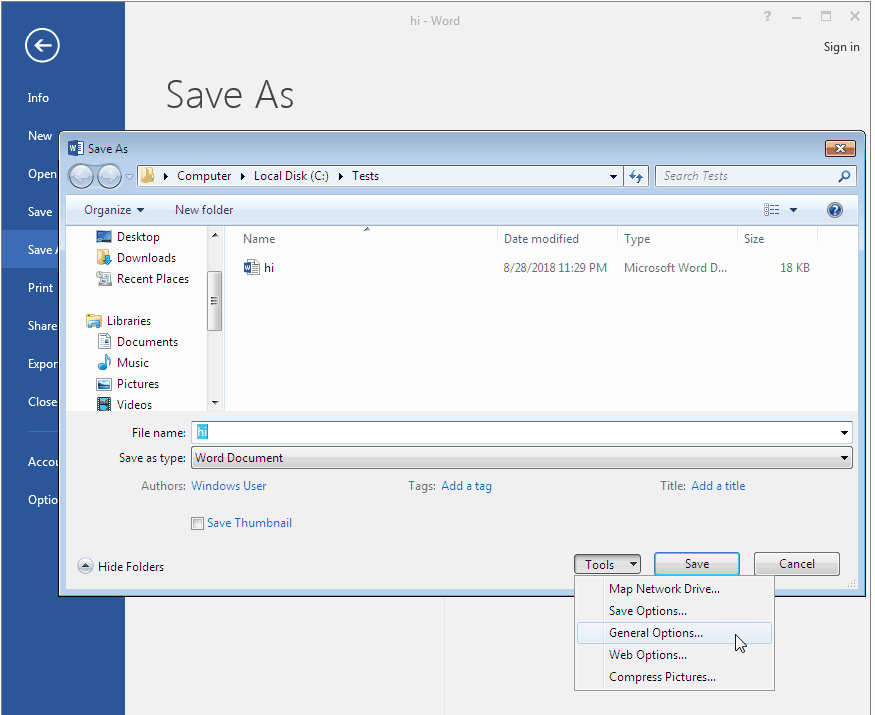
Fig. 4 : Password settings dialog box in Microsoft Word
2. Enter your “Password to Open” in the main box and confirm it in the additional box. The passwords must match. That’s how you make sure no typo crawled in when you entered the password for the first time.
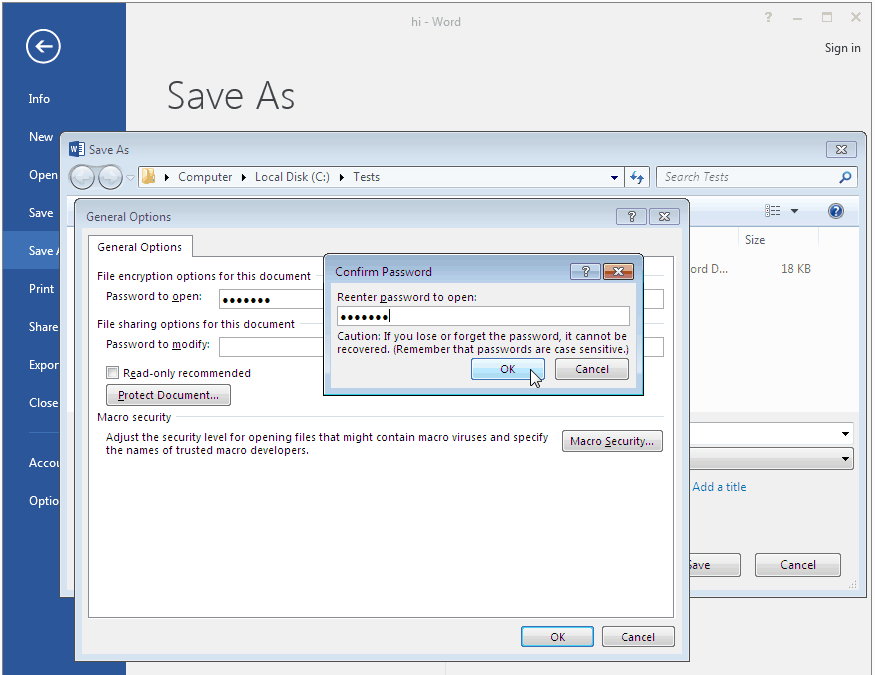
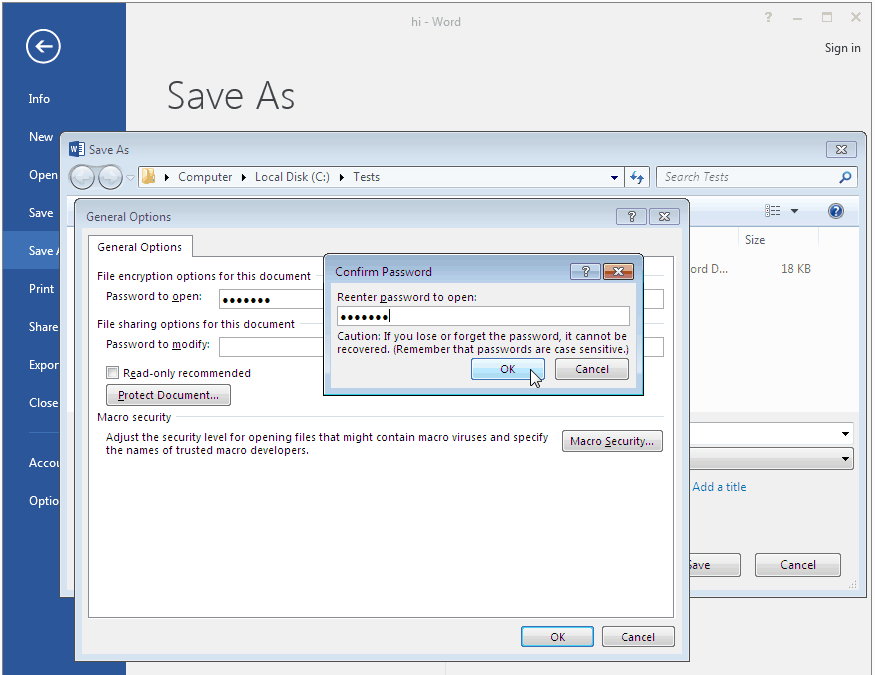
Fig. 5 : Password box in Microsoft Word 2016
You can create a “Password to Modify” in the same dialog box. But keep in mind that any third-party program can instantly remove such a password from any Word file no matter which version you’re using. That kind of password gives poor protection and therefore is quite useless. It’s more of an error-proofing kind of password. :)
3. And we’re done. Enter a file name and save the document. You have successfully encrypted your file with all the data inside. Just make sure you never forget your password.
How to remove a “Password to Open” in a Word file
If you choose not to encrypt your data in a Word document, then all you’ll need to do is just remove your “Password to Open”. Repeat the steps described above (method 1 or 2) but instead of entering a password erase it and save your file:
Fig. 6 : Removing a password in Microsoft Word 2016
The file will be saved as not encrypted and you won’t need a password to open it. Your data won’t be protected, and you won’t face the problem of a lost password.
Password recovery for…
There’s no problem when you know the password – you open a file, delete the password and save. But if you’ve lost the password it might turn out a huge problem. Let’s see how to decrypt a file and recover access to data without a password.
Microsoft warns that losing a password is equivalent to data loss and the company does not provide password recovery tools. Such tools are plenty and widely offered by third-party software developers. Successful password recovery depends on the performance of those programs, their tweaks and tricks and the Word file format.
…Word 6-95
The file format is so old that when it used to be mainstream Microsoft did not really think much of the quality of protection, so now any passwords are found instantly using a low end software tool, for example Accent WORD Password Recovery.
…Word 97-2003 (40-bit encryption key)
Until now the latest version of Word files – Microsoft Word 2016 – still offers as an option to save a document as a file compatible with Word 97-2003. This format has quite a strong encryption mechanism which makes password cracking with straightforward brute force attack really hard and time-consuming. However, duration and efficiency of a password attack depend on the complexity of the password, and its length.
But here’s a trick – you don’t need to search the password. Such files can be decrypted without a password.
Protection is based on a short 40-bit encryption key and, as a rule, it takes much less time (and is more reliable) to find a key rather than a password. With the help of rainbow tables decryption takes no more than a few minutes no matter how complex a password might be.
Some online services, for example, AccessBack.com have successfully taken advantage of that trick.
…Word 2007-2016
Unfortunately, the fairy tale could not last forever – with the appearance of Microsoft Word 2007 file format (docx) Microsoft have been quite successful in fighting against unauthorized access and protecting user data.
So today, while the rate of searching drops with each new version of Word, the only efficient recovery method is brute force attack. Only the best and most powerful software tools are still able to recover lost passwords to Word files, for example Passcovery Suite.
The following functional characteristics have become crucial for the successful recovery of passwords:
- Customization of validation range. Flexible mask configuration mechanism, powerful processing of dictionaries – these are the key features of a highly-efficient password recovery tool. At the same time attempts to use regular brute force attack become more and more futile
- Optimized speed of recovery. An advanced, fine-tuned and perfectly optimized search algorithm lets you recover passwords times faster. And that’s clearly seen when you compare mediocre software tools with the advanced ones
- Acceleration on AMD/NVIDIA graphics cards. Modern GPUs are ideal for searching “Passwords to Open” for Word 2007-2016 documents, and those programs that use GPUs perform times faster. And sometimes tens of times faster, which depends on the CPU/GPU combination in your computer
An example of extended mask
To put it simply, ever since Word 2007 appeared it’s been impossible for an attacker to crack somebody’s password (well, of course, provided that the password is not a trivial word from a dictionary and its length is not three or four characters).
On the contrary however, a file owner’s chances to regain access to data would be pretty high.
If you know what characters your password consists of and in which positions they are used, then you can define an extended (positional) mask. This way you cut off redundant verifications, boost the search process and get a successful result.
Let’s have a look at a case illustrating Passcovery Suite at work:
A lost password consists of 7 or 8 characters, begins with a capital letter – the name of a family member: KVMS; lower case vowels and a few special characters: aeiouy-+_; and ends with three digits.
1. We start Passcovery Suite, open the encrypted file in it, see the info about the file format and type of protection, choose an attack. Select “Brute force attack with extended mask”:
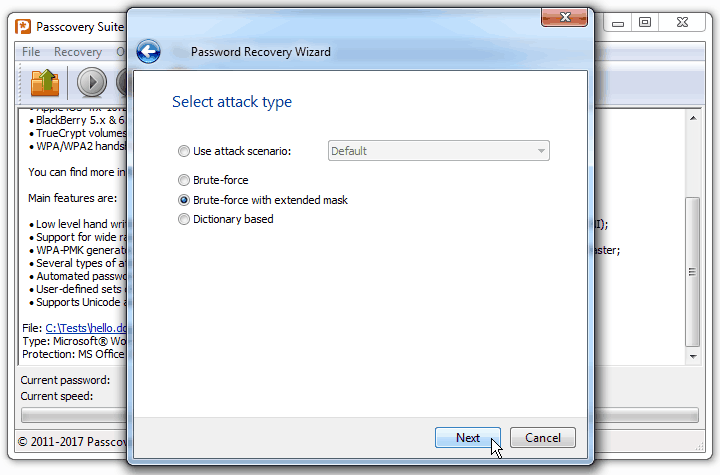
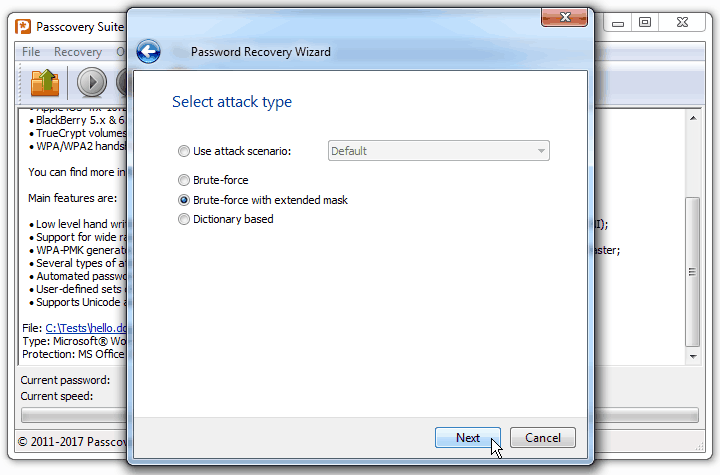
Fig. 7 : Choosing password attack in Passcovery Suite
2. Based on what we know about the password we define character sets that we’re going to use for each position in the password: ?0 – KVMS, ?1 — aeiouy-+_, ?2 - ?d, that is digits (see how to specify an extended mask here). Then we create a mask for generating only suitable passwords, using only relevant character sets — ?0*1?2?2?2; and set the minimum and maximum length of the password — 7-8 characters:
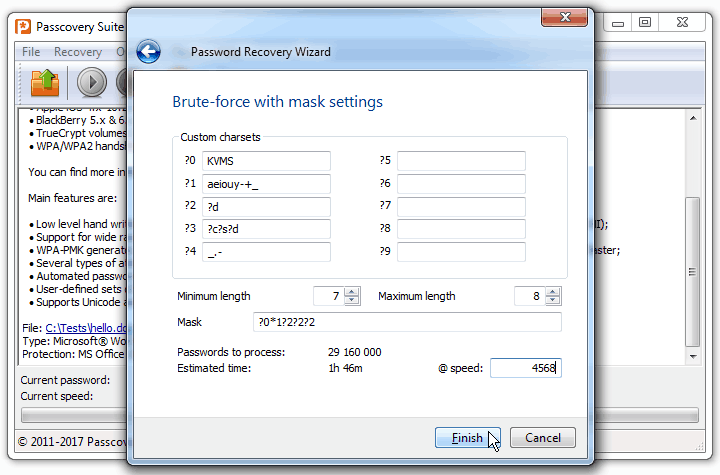
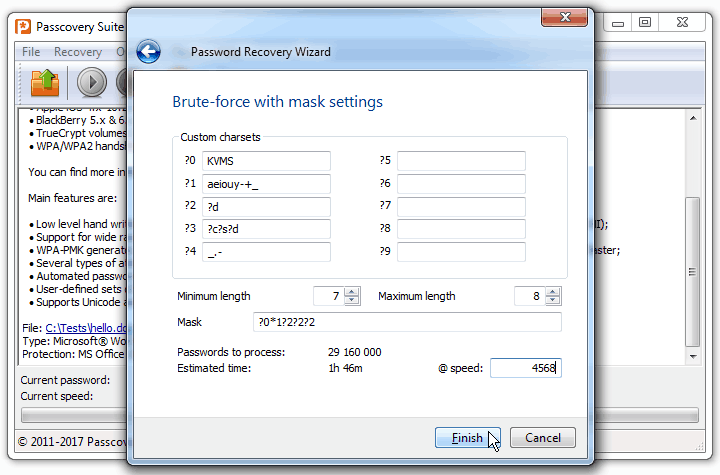
Fig. 8 : Specifying an extended mask using Passcovery Suite
3. And that’s it. You can start the search now. Once the program finds the password it will display it on screen:
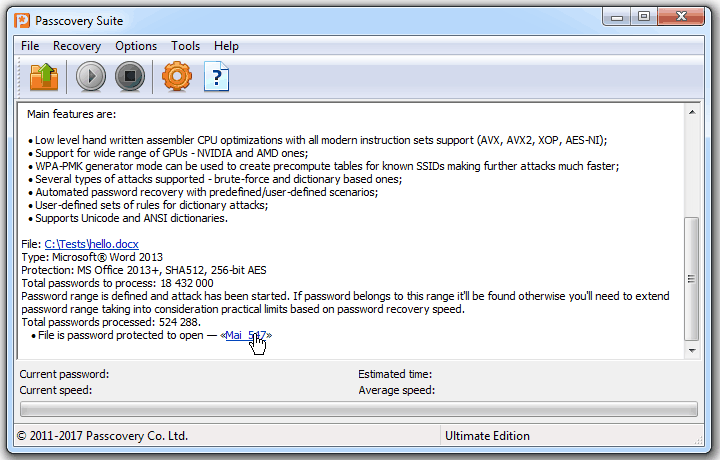
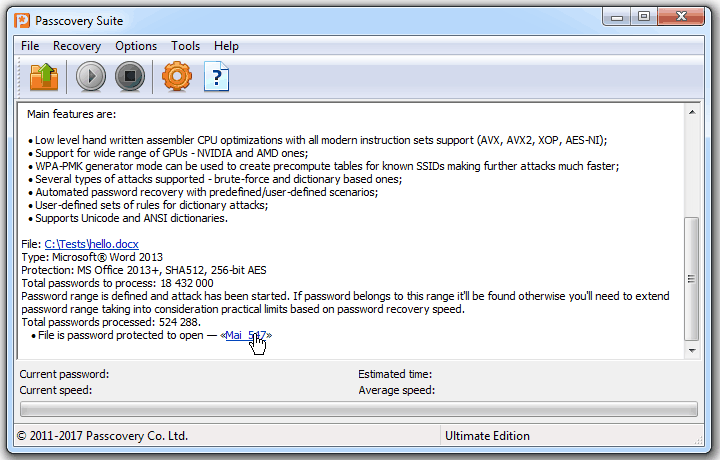
Fig. 9 : Successful password recovery using Passcovery Suite
Find more case studies in the program knowledge base.
Note the number of generated passwords and the expected time for their verification using this mask and without it i.e. with the regular brute force attack:
Fig. 10 : Extended mask vs. brute force attack
That means if an attacker does not know anything about the password, he will either have to check all combinations of characters and pass away long before all options have been verified, or deliberately refuse some of them and risk missing the correct password…