Passcovery Suite – Password Recovery
This is a translation of the article “Jarno Baselier – Passcovery Suite – Password Recovery”, published on the website of Jarno Baselier, a Dutch computer security researcher.
As long as we are using password protection, the problem of lost of passwords will be there and we are going to have to deal with it. Sometimes it can be sufficient to contact the system administrator and ask him or her to reset a forgotten password. However oftentimes you will have to dig deep into your memory trying to recall your password. And if that doesn't work, you have a problem. The only way out would be to "crack the password". And since this is no easy task, I suggest one great option – password recovery software. In this review, I will show you a password recovery program from Passcovery. When you are faced with a problem of a lost password, Passcovery is your best friend you can always rely on. And I am going to show you why. Want to learn more?
Passcovery is a Russian company that first released its products as early as in 1999. In 2010 Passcovery was transformed and modernized and ever since has been an IT company with a staff of avid programmers eager to create the best solutions for password recovery. As a result of the evolution process the company has come to offer a range of high-quality products. Passcovery products are stand-alone tools (for example, specific for each type of Microsoft Office files). See more information at https://passwordrecoverytools.com/. But the flagship product by Passcovery is Passcovery Suite: https://passcovery.com. Passcovery Suite facilitates recovery of passwords for many types of files, such as Microsoft Office/OpenOffice, Adobe PDF, WinRAR, ZIP, Apple iOS, etc.
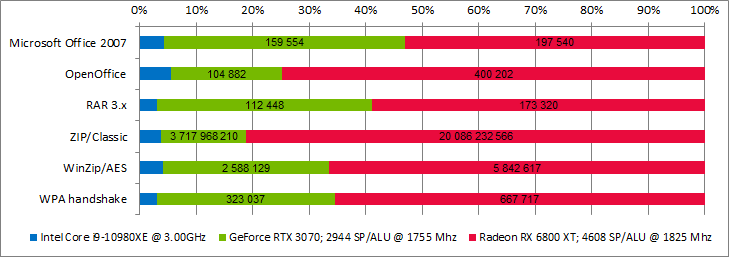
Not all password recovery programs support GPU acceleration. Passcovery products do support GPU acceleration, both on NVIDIA and AMD graphics cards. The GPU computing technology enables the program to perform testing and searching functions at the maximum speed which boosts the password cracking process. The standard license of Passcovery Suite supports a single GPU. The Professional license allows using two GPUs. And if you have really cool hardware with a multiple GPUs, the Ultimate license would be the best choice as it supports all GPUs available in the Windows system.
Files of versions prior to Microsoft Office 2003 (and saved in compatible format) use weaker encryption (MD5 with 40-bit RC4). Passcovery products enable the user to crack any file protected with this type of encryption with a 100% guarantee (by using rainbow tables or encryption key search). For later versions of Microsoft Office formats other options are available. Among which are of course dictionary attack and brute force attack, but also the following:
- Mask attack
- Extended (Positional) mask attack
- Dictionary Merge and Mutation Attack
Below I am taking a closer look at these three original techniques.
Mask Attack
A dictionary attack uses a targeted technique of successively trying all the words from a pre-arranged list of values. And with a brute force attack, the attacker just tries the combination of letters and numbers to generate a password sequentially. With a mask attack the user creates masks to exploit password habits. A common habit is to use a combination of one's favorite words, letters and symbols. Suppose this is my password:
Jarno##2000
It is highly likely that somewhere I should also have a password like that one:
Jarno$$2010
As you can see, these passwords consist of 5 letters, 2 special characters and 4 digits. In a mask attack we exploit this information which makes our attack more accurate and efficient. In this case, the first 5 and last 4 positions are not occupied by special characters, and the 2 middle positions are neither numbers nor letters. A reduced set of characters and positional restrictions make the mask attack a much faster and efficient technique. A mask attack is always much better than a simple brute force attack. The snag is that you need to have at least some idea (or know a few possible versions) of the password structure.
Extended (Positional) Mask Attack
An extended mask attack is an advanced version of a regular mask attack. An extended mask attack enables the user to define specific character sets individually for each position in the password which makes it even more effective. In a regular mask attack, the initial 5 positions can only be occupied by the entire sets of letters [a-z | A-Z]. If you know something more specific about the password, you can use this knowledge to configure a smaller range of letters for each password position (for example, [j, J] for the initial position). This is actually what makes the attack even more effective.
Dictionary Merge and Mutation Attack
A dictionary attack can also be of great use. However Passcovery Suite (like all other Passcovery programs) offers an advanced dictionary attack with merging and mutation. This means that Passcovery programs are smart enough to combine different dictionaries and generate new passwords from various wordlists. So you can, for example, use a few dictionaries with postal codes, years, and last names. And Passcovery will use the lists of values to generate all possible combinations. And that's not all. By using a macro language to describe mutations, we can make Passcovery change words. Thus, we can set a rule that all words should begin with a capital letter, in addition to their original spelling in dictionaries, where all the words begin with lowercase letters. That means Passcovery creates extra ad hoc dictionaries so you don't have to.
All Passcovery programs support multilingual dictionaries in Unicode format. Program interface is available in 8 different languages. Along with the regular Windows GUI, the software supports command line interface (CLI).
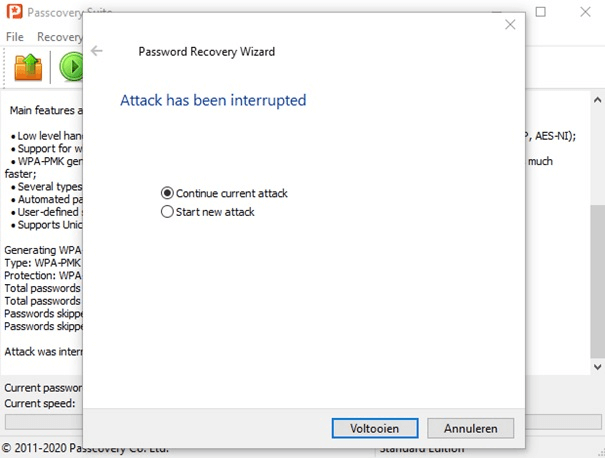
An important feature of the software is the ability to save the current attack status and resume it later from where we left off. This way you save your time.
Well, enough said. Of course, we all want to see how those features work. Passcovery was so kind as to grant me a license for its flagship product. So, let's get it started with Passcovery Suite.
Passcovery Suite Installation
First, download the software from Passcovery website, and then install it by taking the simple "Next-Next-Done" steps.
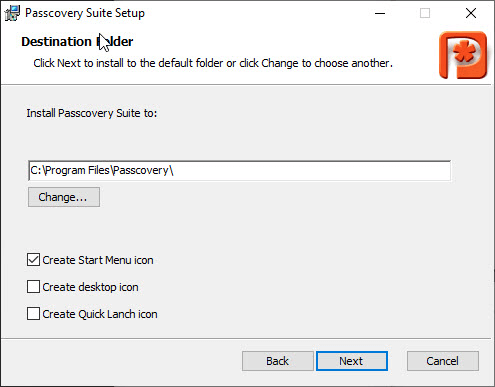
During installation you'll be asked to enter the registration key to activate the full version. If you skip this step, you'll end up with the demo version only.
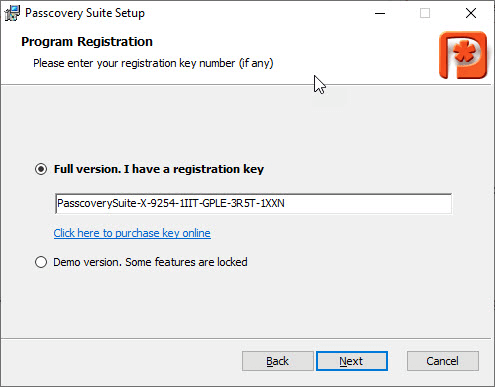
When you run Passcovery Suite for the first time with the registration key having been entered during installation, make sure you activate the license:
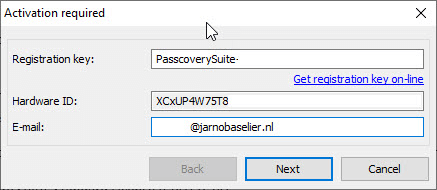
Just complete a few steps and your Passcovery Suite will be ready to use:
Using Passcovery Suite
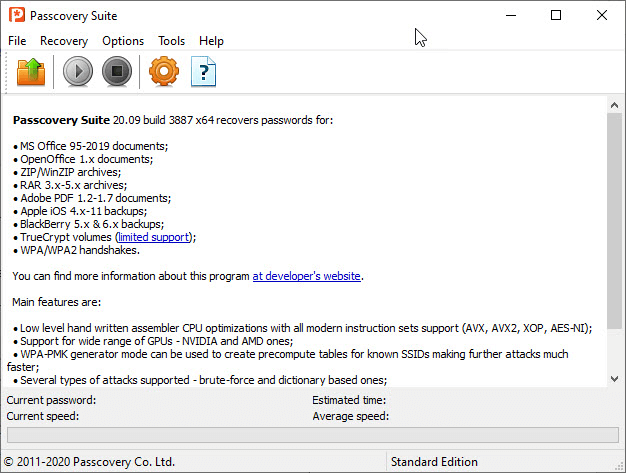
Now that Passcovery Suite is installed and activated, it's time to crack passwords. But first, let's take a look at the interface.
The menu bar is very convenient. It has an upload folder icon, a play button to start cracking, and a stop/pause button to put the process on hold. Settings are easily accessible and in the case of any problem there is a help button.
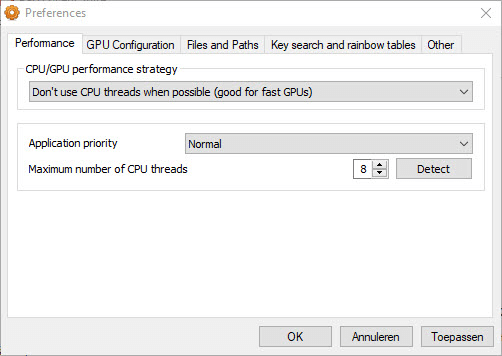
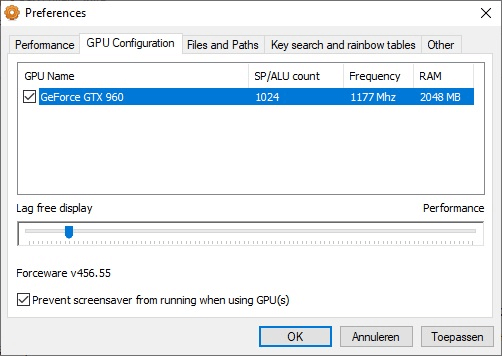
In the settings window the user can define the algorithm, in particular, the CPU and GPU utilization scenarios. Each of the scenarios affects the interaction of hardware units. However when you are using Passcovery Suite on a regular PC, the default settings will be suit the best. I am using a PC with a good graphics card, so my settings look like this:
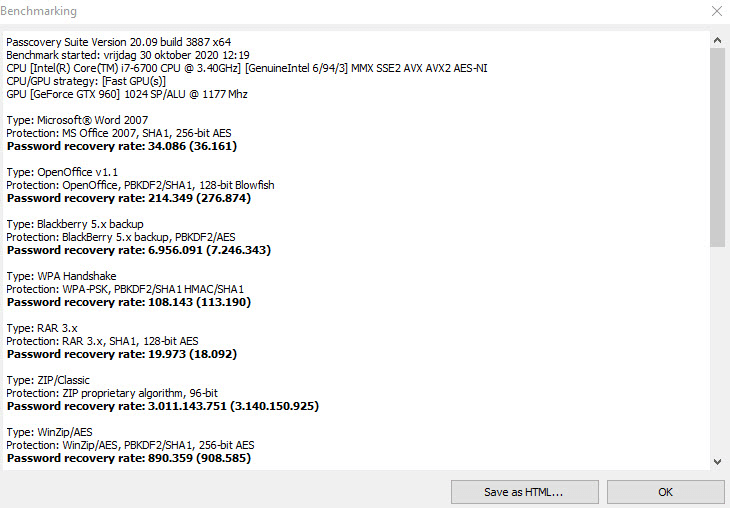
Then, to get an idea of the speed of a brute force attack (and review the defined settings), you might also run the “Benchmark” tool (see the “Tools” menu):
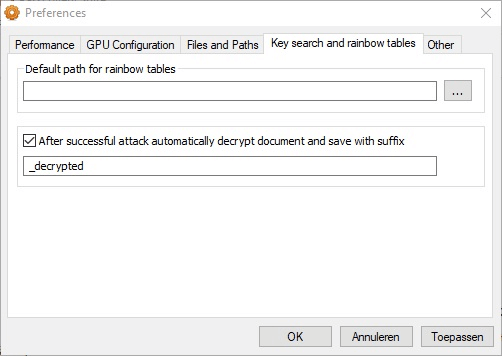
In the “File” tab, you'll find a WPA-PMK generator that generates a file based on your SSID and then attempts to crack the WPA password. Passcovery Suite makes it easy to crack WPA passwords in automatic mode. As you can see, you may restart an interrupted attack or resume it later from where you left off:
An important feature of Passcovery Suite is the “Rules Editor” (see “Tools” menu). This tool enables you to create the rules according to which passwords from dictionaries will be changed. The “Rules Editor” allows to configure processing of four dictionaries at once and gives a clear preview of the function of each particular rule:
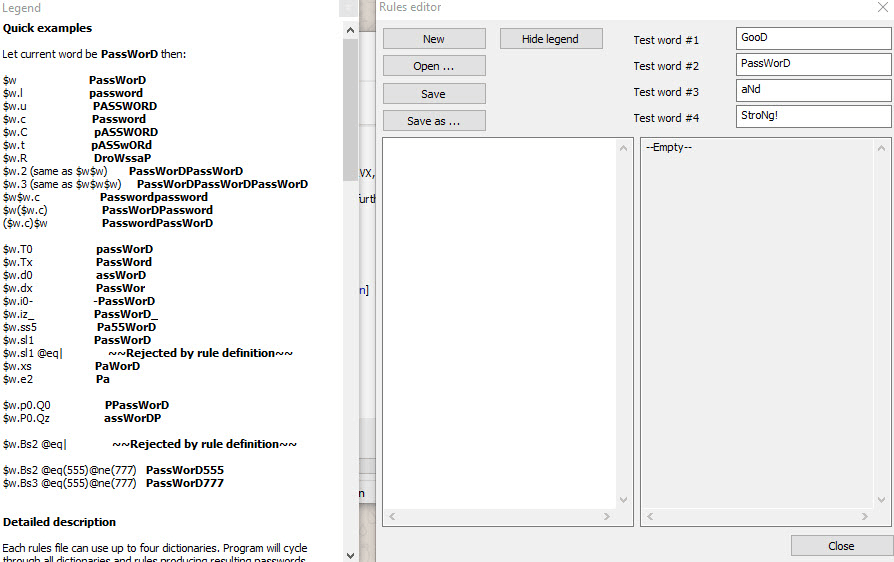
In the upper right corner you will find the test words (each one representing one of the four dictionaries). The field in the lower left corner is the “Rules Editor”, and opposite in the right corner - the resulting value, that is you see in real time how those rules modify the currently tested words.
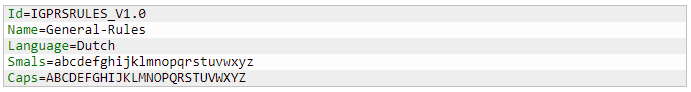
A rules file always starts with a header that specifies the current version, its name, and which uppercase and lowercase letters conform to our logic:
And then we move to the rules in the [Rules] window:
Here's what I'd like to test:
- Each password as it is in the dictionary without any mutation ($w denotes passwords from dictionary 1)
- Each password with the first letter capitalized (I am going to use $w.c)
- Each password with upper-case letters ($w.u)
- Each password ending with "2021" ($w.Bs2 @eql(2021))
- Passwords from the second dictionary with the same rules ($x denotes passwords from dictionary 2)
- Words from dictionary 1 and dictionary 2 combined into one password (and vice versa). Here is how you do it: $w$x and $x$w
Then you get the following rules:
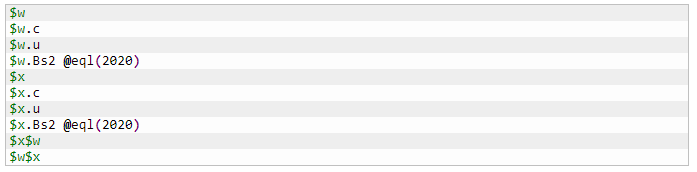
The “Rules Editor” uses the following language:
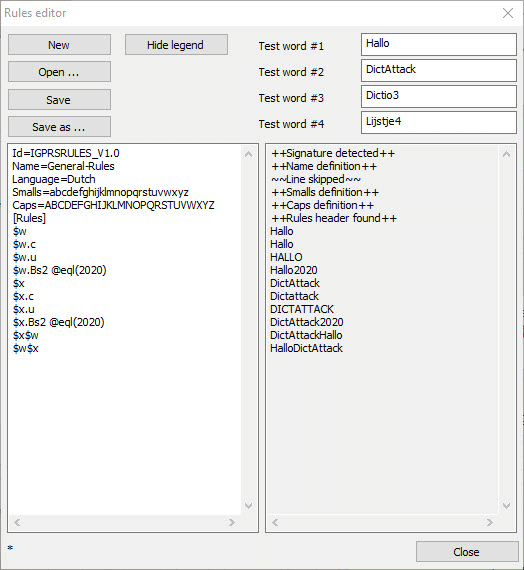
To enable dictionary 3 and 4, use $y and $z. Once you're done describing the set of rules, save it to a file, and use later when running an attack. That is one plain and simple way to customize dictionary attack by setting the rules you need.
Once all the rules are defined, we can actually start cracking the password.
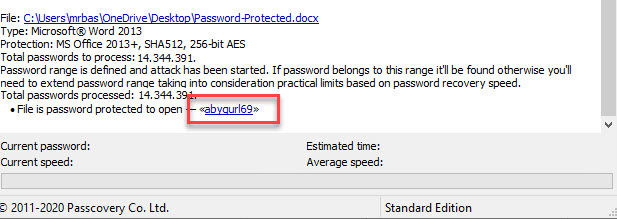
First we are going to save a document with the password “abygurl69”. This password is found in a well-known dictionary “rockyou.txt”:
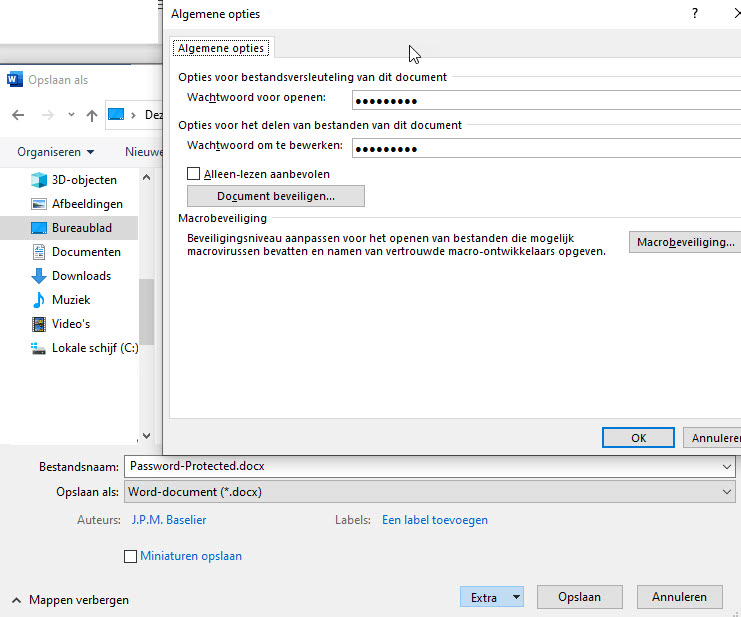
Now we are going to run a regular dictionary attack using the words from "rockyou.txt". As you open a protected file, Passcovery Suite displays the information about the type of encryption used:
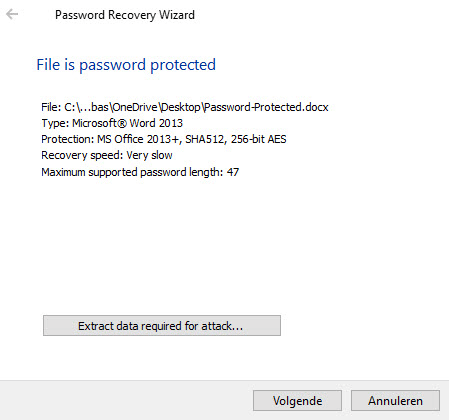
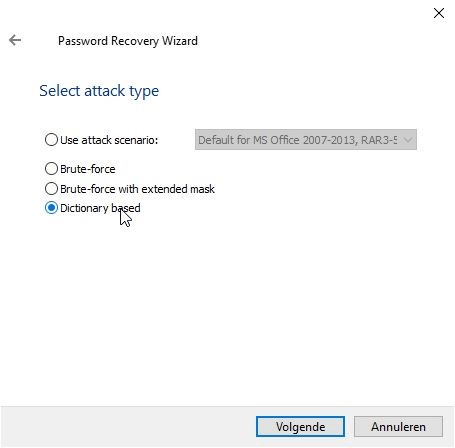
By clicking on “Extract data required for attack” you can save a .bin file which might be useful in another password cracker. Actually, this is where all the hashes and data required for the attack are stored. Since we only prefer to use Passcovery Suite, we need to click “Next” and select “Dictionary Attack”. By default, a Passcovery pre-defined scenario is selected with the minimum set of values for a brute force attack for this type of files:
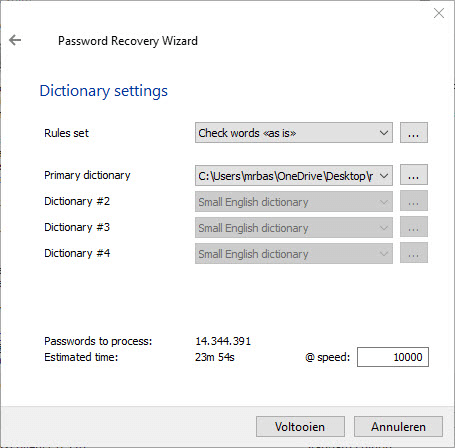
Now, you may customize a set of rules and select a dictionary. Passcovery Suite comes with a few basic dictionaries and a number of pre-defined sets of rules. So we just choose the dictionary named “rockyou.txt”, and proceed without editing the rules and leaving them as is:
As you click “Done”, Passcovery Suite will start working.
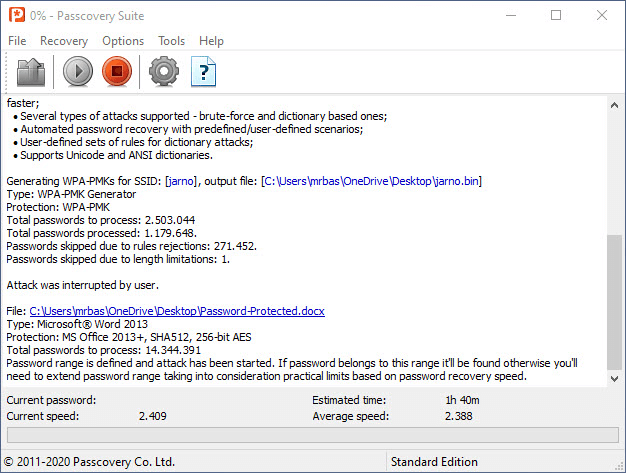
It took Passcovery Suite about 1.5 hours to find the password. The password was at the bottom of the list, so Passcovery went through 14 million passwords in 90 minutes.
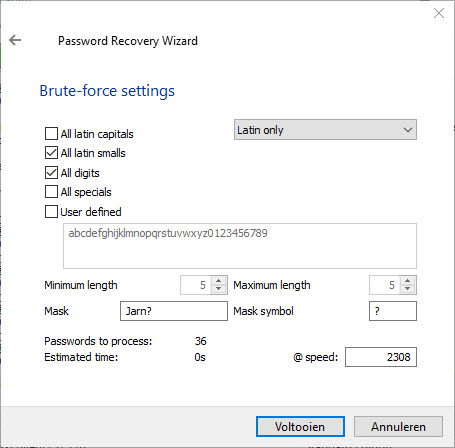
Similarly, you can choose to run a brute force attack. When setting up a brute force attack, it is important to select the symbols to be used. All these options are available in Passcovery programs. Make sure you specify the minimum and maximum length of passwords before you run a brute force attack. See the number of passwords to be tested in the counter below. Also, you can set up a simple mask. For example, if you know a part of the password, then mark the unknown characters with a question mark:
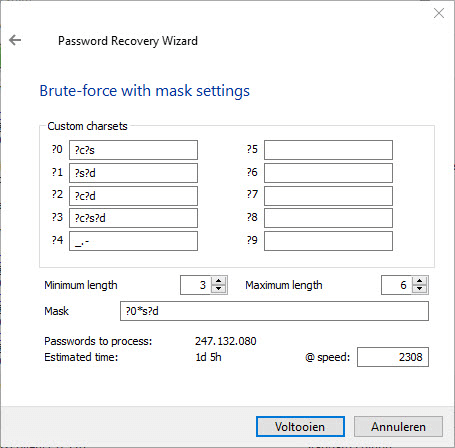
Besides, a brute force attack with an extended mask is also an option. The advantage of this type of attack is that it allows setting a more detailed mask. Below are the symbols used in an extended mask and their designation:
- ?c - all uppercase Latin letters
- ?s - all lowercase Latin letters
- ?d - all digits
- ?e - all special characters (34 characters, from space character (0x20) to 0x7F)
- ?a - all printable characters (96 characters from 0x20 to 0x7F, in arranged order)
- ?? - the symbol “?”
A few examples:
Mask: ?a
Attack symbols: ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789 !"#$%&'()*+,-./:;<=>?[\]^_`{|}~ (and 0x7F)
Mask: ?s
Attack symbols: abcdefghijklmnopqrstuvwxyz
Mask: ?s?d
Attack symbols: abcdefghijklmnopqrstuvwxyz0123456789
Mask: ?s?c
Attack symbols: abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ
In this mask, each question mark denotes a character position in the password. Suppose we need to crack a 5-character password with a lowercase letter in each position. The mask will look like this:
?s?s?s?s?s
Apart from the question mark, to denote a position in the password you can also use an asterisk – *. An asterisk does not mean just 1 position, but all implicit positions within a given length. So, if I had to test a word of 5 characters, where the first and last characters are lowercase letters, and there are digits in between, then the mask will be like this:
?s*d?s
If necessary, you can also create your own character sets. Suppose we need to test a character in the password with uppercase and lowercase letters. In that case we will create our own character set using "?c?d". We'll have to mention it in the mask with the number of your charset. For instance, "?0".
Say our character set #0 consists of uppercase and lowercase letters (?c?d), and we need to test a word of 5 letters, the first character of which should be both uppercase and lowercase letters (this is exactly the character set #0 we just created), and the remaining 4 are only lowercase letters. Then the mask will be the following:
?0?s?s?s?s
, or:
?0*s
See an example below:
Conclusion
Passcovery has been in this business for more than 20 years, you can tell. Passcovery tools have a pleasant-looking interface, featuring professional options and are easy to use. I would very much like to see a Linux-compatible edition and equip my "Kali" machine with a handy password cracker for all file types. Anyway, this is definitely one of the best and most efficient password crackers for Windows. Excellent GPU-enabled computing and the ability to resume cracking are the features any user would highly appreciate. Although Passcovery Suite is not the cheapest product, rest assured that you are getting a high-quality solution that offers flexible customization options and accommodates all your needs and ideas.